Should CWE Use Same Computers as Those Used by Windows XP
The Red Hat Enterprise Linux variant requires computer hardware to meet several conditions for a fully successful and operational installation. Some of these core requirements include a Random Access Memory (RAM) of 2GB minimum, a Hard Drive of 4GB as well as 2.0 USB ports. Fortunately, the computer hardware in use for the Windows XP meets all these conditions since there is 2GB RAM is, Hard Disk of 80GB and four 2.0 USB ports. Furthermore, the hardware processor is that of Intel Core 2. Such types of processors are considered to be of the minimum capacity possible for the operations of Red Hat Enterprise Linux (RHEL).
Moreover, several of updates have been released with an objective of supporting Intel processors by RHEL. With the current hardware meeting these requirements, the need to acquire new hardware eliminates. The firm will thus avoid incurring extra cost for the procurement of new computer hardware as the Windows XP operating system could be substituted with Linux on the same machines. However, it appears that the speed of the Ethernet card is quite low and would require an upgrade to above 100Mbps.
Get a price quote
Planning for Installation
There are no major approaches that could be used for the upgrading of an existing Windows XP system to Red Hat Enterprise Linux. Both procedures include clean installation, an in-place upgrade. The following explanation may be adopted regardless of the choice of procedure. A clean installation could occur by putting in place a back-up for all the information on the system, and later by formatting disk partitions. Then, installation of Red Hat Enterprise Linux from the media should be done but before restoring the user data from the backup. On the other hand, the in-place upgrade involves fitting a new system on the computer without necessarily removing the old one. That means both Windows XP and Red Hat Enterprise Linux may operate from the same computer.
The process requires migration utilities to be available. For the Red Hat Linux, an assessment of the current system is core to identify potential challenges that could occur during the upgrade. That will perform slight fixes as well as modifications on the system. Moreover, the upgrade tool of the Red Hat will download and do the upgrading. The process could involve numerous troubleshoots along with planning performed, however, only in instances when there are no other choices.
Hardware to Use during Installation
As considering the hardware to be used, the costs should be studied. The expenses ought to include an upgrade of the hardware to make them compatible with the installation as well as training on using a new operating system. Moreover, its installation should justify all or the majority of the reasons why it is being performed. Red Hat Linux is known for its safety measures against malware which is core (Boko? et al., 2015). The core hardware, in this case, includes a CPU, CD drive, a keyboard as well as a monitor.
The installation of Red Hat on the computers that previously had Windows XP as the operating system may also require an upgrade of the latter. For the devices where Windows XP has been installed, a Red Hat Linux 7.3 CD could be inserted and directives appearing on the monitor followed. One should choose to remove default Linux Partitions present on the system during partitioning due to prior absence of such partitions.
The popped up screen would be:
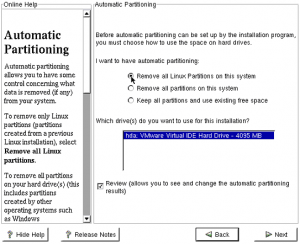
When choosing the automatic partitioning option, a warning could appear about likely loss of the data. However, since it is the first installation of Linux, no actual data can be lost. The ‘Next’ button should then be pressed.
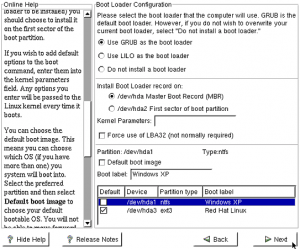
The appearing display will hence show break down of the hard drive by Linux installer as shown:

For the Windows XP partition, it will be depicted under /dev/hda1, which is a type of HPFS or NTFS. Just below, there are the four Linux partitions. The first appears as ext3, which is a boot partition. The others are Linux File System and Swap partition, which is significant to all the Linux systems (Hellums, 1999). At this point, a configuration of the boot loader named GRUB is done. The ‘Next’ button should then be pressed. The following screen appears for the boot configuration:
When Red Hat Enterprise Linux is completely installed, the system restarts. The display on the monitor is as follows:

The user should choose the Red Hat Linux option.
Logging to Systems
When the computer boots, the screen will display two Operating Systems present. At this juncture, the user has to use the allow keys of the keyboard to select the preferable system (in this case, Linux) and press Enter. After the opening up, the user-account login and password should be entered to receive access. The user is thus allowed to use the computer for various purposes including online ones. There can be more than one on the computer in order to guarantee to data security of each person who uses the device.
New to BestWritingHelp?
Get your 15% OFF the first order! Code firstorder
Receiving IP Address
The files involved in the interface configuration direct software interfaces for each network device. When the system is booting, the files are used in order to determine the interfaces that should appear as well as the way they should be configured. The files are usually under the name ifcfg – <name>. The <name> belongs to the device that is controlled by the configuration file controls.
The interfaces could be either Ethernet or IP. When using the Red Hat Linux, it becomes easier to make a connection to several hosts and networks applying a secured IP connection, which is identified as IPsec. Other forms of interfaces are such as Channel Bonding where administrators will get the opportunity to bring several networks together via the use of boarding kernel module (Hellums, 1999). That permits two or more net interfaces to operate as one while concurrently provides redundancy as well as increased bandwidth.
How DNS will be accessed by the CWE systems
Then, the software will perform a reverse Domain Name System (DNS) resolution on the IP address. The aim of that is to assist in obtaining the hostname as well as ensuring a proper security decision. However, it fails to accurately provide the IP address with a true association with the hostname. Should a DNS server be compromised, the names in the system might also be misreported or spoofed, thus making it difficult for software detection (Ghori, 2015). An attacker controlling the server would hence force the server to make an arbitrary return to the hostname when a reverse DNS resolution is performed.
That would essentially allow such an attacker to bypass authentication, leading to the recording of an inappropriate hostname in the log-in files with the objective of hiding their activities or performing other attacks. Invaders into the system could spoof DNS names through either a compromise of the DNS server as well as modification of its records, popularly known as DNS cache poisoning or via a legitimize control of the DNS server that is associated with the target IP address.
How CWE Securely Shares Files
Handling of Printing
CWE solutions could be provided for printing hardware. During printing, the utilization of modern technology is necessary for quick efficient process and clear documents. CWE offers a wide range of printing formats allowing printing of different types of materials. Further, the consistency in the printing work is maintained for actual projects since the color match is always enhanced. These simplify printing as well as eliminate the previously existing complexities.
Encrypted Data
Data sent over a network is at the risk of being compromised while transmitting. Attackers may read or perform some modifications should such information be sent as plaintext, or weak encryption be used. To ensure protection and avoid such instances, strong encryption is necessary to prevent the network invaders from accessing important confidential business information or making an alteration of any kind. Encryption offers some degree of security for data from being controlled by a wrong person or lost unnecessarily.
